Arslan, Şefik Şuayb
Loading...
Profile URL
Name Variants
Arslan, Şuayb Şefik
Arslan Suayb S.
Arslan, Şuayb Ş.
Arslan , Şuayb Şefik
Arslan Suayb S.
Arslan, Şuayb Ş.
Arslan , Şuayb Şefik
Job Title
Email Address
arslans@mef.edu.tr
Main Affiliation
02.02. Department of Computer Engineering
Status
Current Staff
Website
ORCID ID
Scopus Author ID
Turkish CoHE Profile ID
Google Scholar ID
WoS Researcher ID
Sustainable Development Goals
 1
1NO POVERTY
0
Research Products
 2
2ZERO HUNGER
0
Research Products
 3
3GOOD HEALTH AND WELL-BEING
0
Research Products
 4
4QUALITY EDUCATION
0
Research Products
 5
5GENDER EQUALITY
0
Research Products
 6
6CLEAN WATER AND SANITATION
0
Research Products
 7
7AFFORDABLE AND CLEAN ENERGY
0
Research Products
 8
8DECENT WORK AND ECONOMIC GROWTH
0
Research Products
 9
9INDUSTRY, INNOVATION AND INFRASTRUCTURE
0
Research Products
 10
10REDUCED INEQUALITIES
0
Research Products
 11
11SUSTAINABLE CITIES AND COMMUNITIES
1
Research Products
 12
12RESPONSIBLE CONSUMPTION AND PRODUCTION
0
Research Products
 13
13CLIMATE ACTION
0
Research Products
 14
14LIFE BELOW WATER
0
Research Products
 15
15LIFE ON LAND
1
Research Products
 16
16PEACE, JUSTICE AND STRONG INSTITUTIONS
0
Research Products
 17
17PARTNERSHIPS FOR THE GOALS
0
Research Products

This researcher does not have a Scopus ID.

This researcher does not have a WoS ID.

Scholarly Output
43
Articles
17
Views / Downloads
9440/61932
Supervised MSc Theses
0
Supervised PhD Theses
0
WoS Citation Count
127
Scopus Citation Count
197
Patents
11
Projects
3
WoS Citations per Publication
2.95
Scopus Citations per Publication
4.58
Open Access Source
17
Supervised Theses
0
| Journal | Count |
|---|---|
| 26th IEEE Signal Processing and Communications Applications Conference, SIU 2018 | 3 |
| 2021 29th Signal Processing and Communications Applications Conference (SIU) | 2 |
| 2022 7th International Conference on Computer Science and Engineering (UBMK) | 2 |
| IEEE International Symposium on Information Theory (ISIT) -- JUN 26-JUL 01, 2022 -- Espoo, FINLAND | 2 |
| Journal of Vision | 2 |
Current Page: 1 / 7
Scopus Quartile Distribution
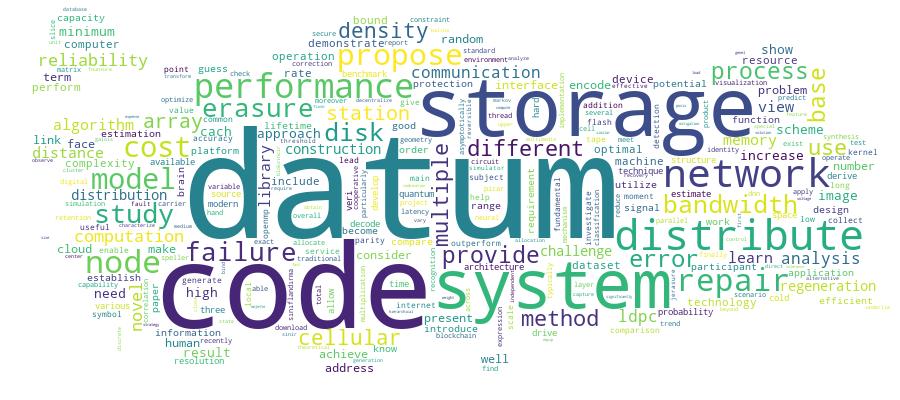
Competency Cloud
43 results
Scholarly Output Search Results
Now showing 1 - 10 of 43
Article Citation - WoS: 2Citation - Scopus: 2TALICS3 : Tape library cloud storage system simulator(Elsevier, 2024) Peng, James; Arslan, Şuayb Şefik; Göker, TurguyHigh performance computing data is surging fast into the exabyte-scale world, where tape libraries are the main platform for long-term durable data storage besides high -cost DNA. Tape libraries are extremely hard to model, but accurate modeling is critical for system administrators to obtain valid performance estimates for their designs. This research introduces a discrete- event tape simulation platform that realistically models tape library behavior in a networked cloud environment, by incorporating real -world phenomena and effects. The platform addresses several challenges, including precise estimation of data access latency, rates of robot exchange, data collocation, deduplication/compression ratio, and attainment of durability goals through replication or erasure coding. Using the proposed simulator, one can compare the single enterprise configuration with multiple commodity library configurations, making it a useful tool for system administrators and reliability engineers. This makes the simulator a valuable tool for system administrators and reliability engineers, enabling them to acquire practical and dependable performance estimates for their enduring, cost-efficient cold data storage architecture designs.Conference Object Citation - Scopus: 4Openmp and Posix Threads Implementation of Jerasure 2.0(IEEE, 2017) Arslan, Şuayb Şefik; Le, Hoa; Landman, Joseph; Goker, TurguyIn shared memory multiprocessor architectures, threads can be used to implement parallelism. POSIX threads (pthreads) is a low-level bare-bones programming interface for working with threads. Therefore, we have extremely fine-grained control over thread management (create/join/etc), mutexes, and so on. On the other hand, openMP, as a shared-memory standard, is much higher level and portable interface which makes it easier to use multi-threading capability and obtain satisfactory performance improvements. Since pthreads is more flexible, it helps programmers gain more control on performance optimizations. Jerasure 2.0 erasure coding library has encoding/decoding engines which comprise independent "for" loop iterations and hence possess huge potential for multi-threaded processing. In this short paper, we investigate multi-threaded implementations of encoder/decoder pair of Jerasure 2.0 using two different technologies: OpenMP and pthreads. We constrain our changes to a minimum possible and compare the pure encoding/decoding performance with respect to each other as well as against that of the original single-threaded version by running them on two different server systems.Conference Object Citation - Scopus: 2Ssqem: Semi-Supervised Quantum Error Mitigation(IEEE, 2022) Sayar, Alperen; Arslan Suayb S.; Çakar Tuna; Arslan, Suayb S.; Cakar, TunaOne of the fundamental obstacles for quantum computation (especially in noisy intermediate-scale quantum (NISQ) era) to be a near-term reality is the manufacturing gate/measurement technologies that make the system state quite fragile due to decoherence. As the world we live in is quite far away from the ideal, complex particle-level material imperfections due to interactions with the environment are an inevitable part of the computation process. Hence keeping the accurate state of the particles involved in the computation becomes almost impossible. In this study, we posit that any physical quantum computer sys-tem manifests more multiple error source processes as the number of qubits as well as depth of the circuit increase. Accordingly, we propose a semi-supervised quantum error mitigation technique consisting of two separate stages each based on an unsupervised and a supervised machine learning model, respectively. The proposed scheme initially learns the error types/processes and then compensates the error due to data processing and the projective measurement all in the computational basis. © 2022 IEEE.Conference Object Citation - WoS: 5Citation - Scopus: 7Cloud2hdd: Large-Scale Hdd Data Analysis on Cloud for Cloud Datacenters(IEEE, 2020) Zeydan, Engin; Arslan, Şefik ŞuaybThe main focus of this paper is to develop a distributed large scale data analysis platform for the opensource data of Backblaze cloud datacenter which consists of operational hard disk drive (HDD) information collected over an observable period of 2272 days (over 74 months). To carefully analyze the intrinsic characteristics of the hard disk behavior, we have exploited a large bolume of data and the benefits of Hadoop ecosystem as our big data processing engine. In other words, we have utilized a special distributed scheme on cloud for cloud HDD data, which is termed as Cloud2HDD. To classify the remaining lifetime of hard disk drives based on health indicators such as in-built S.M.A.R.T (Self-Monitoring, Analysis, and Reporting Technology) features, we used some of the state-of-the-art classification algorithms and compared their accuracy, precision, and recall rates simultaneously. In addition, importance of various S.M.A.R.T. features in predicting the true remaining lifetime of HDDs are identified. For instance, our analysis results indicate that Random Forest Classifier (RFC) can yield up to 94% accuracy with the highest precision and recall at a reasonable time by classifying the remaining lifetime of drives into one of three different classes, namely critical, high and low ideal states in comparison to other classification approaches based on a specific subset of S.M.A.R.T. features.Conference Object Citation - WoS: 14Citation - Scopus: 40An Overview of Blockchain Technologies: Principles, Opportunities and Challenges(IEEE, 2018) Arslan, Şuayb Şefik; Mermer, Gültekin Berahan; Zeydan, EnginBlokzincir, toplumumuzun birbiriyle iletişim kurma ve ticaret yapma biçiminde devrim yapma potansiyeline sahip, yakın zamanda ortaya çıkmış olan bir teknolojidir. Bu teknolojinin sağladığı en önemli avantaj aracı gerektiren bir oluşumda güvenilir bir merkezi kuruma ihtiyaç duymadan değer taşıyan işlemleri değiş tokuş edebilmesidir. Ayrıca, veri bütünlüğü, dahili orijinallik ve kullanıcı şeffaflığı sağlayabilir. Blokzincir, birçok yenilikçi uygulamanın temel alınacağı yeni internet olarak görülebilir. Bu çalışmada, genel çalışma prensibi, oluşan fırsatlar ve ileride karşılaşılabilecek zorlukları içerecek şekilde güncel blokzincir teknolojilerinin genel bir görünümünü sunmaktayız.Conference Object Citation - WoS: 1Citation - Scopus: 1Adaptive Boosting of Dnn Ensembles for Brain-Computer Interface Spellers(IEEE, 2021) Çatak, Yiğit; Aksoy, Can; Özkan, Hüseyin; Güney, Osman Berke; Koç, Emirhan; Arslan, Şuayb ŞefikSteady-state visual evoked potentials (SSVEP) are commonly used in brain computer interface (BCI) applications such as spelling systems, due to their advantages over other paradigms. In this study, we develop a method for SSVEP-based BCI speller systems, using a known deep neural network (DNN), which includes transfer and ensemble learning techniques. We test performance of our method on publicly available benchmark and BETA datasets with leave-one-subject-out procedure. Our method consists of two stages. In the first stage, a global DNN is trained using data from all subjects except one subject that is excluded for testing. In the second stage, the global model is fine-tuned to each subject whose data are used in the training. Combining the responses of trained DNNs with different weights for each test subject, rather than an equal weight, provide better performance as brain signals may differ significantly between individuals. To this end, weights of DNNs are learnt with SAMME algorithm with using data belonging to the test subject. Our method significantly outperforms canonical correlation analysis (CCA) and filter bank canonical correlation analysis (FBCCA) methods.yl-bitirme-projesi.listelement.badge The Passanger Load Factor Prediction of Airline Transport(MEF Üniversitesi, Fen Bilimleri Enstitüsü, 2017) Karakoç, Kalender; Arslan, Şuayb Ş.Turkish Airlines is one of the most preferred leading European air carriers with global network coverage thanks to its strict compliance with flight safety, reliability, product line, service quality and competitiveness. Turkish Airlines maintains its identity as the flag carrier of Turkey.yl-bitirme-projesi.listelement.badge Loaction Based Recommendation System Using Flickr Geotagged Photos(MEF Üniversitesi, Fen Bilimleri Enstitüsü, 2018) Çakar, Erbil; Arslan, Şuayb Ş.Flickr is a worldwide photo sharing application. In this project, photos with location information provided by Flickr will be used. By utilizing this location information, a recommendation system that recommends users the most suitable photo shooting locations based on their historical data will be designed. During this system design phase, different methodologies will be tried and a research will be conducted on the methods that provide the most appropriate solution to the problem.yl-bitirme-projesi.listelement.badge Humpback Whale Indentification With Convolutional Neural Networks(MEF Üniversitesi, Fen Bilimleri Enstitüsü, 2018) Can, Duygu; Arslan, Şuayb Ş.The migration patterns of humpback whales are tracked with conventional photoidentification techniques for decades. The distinct markings on whale flukes serve as unique fingerprints for these creatures. This study aims to identify humpback whales according to their fluke images using ResNET, a deep neural network architecture to help the conservation efforts for this endangered species by automatizing the process. We experimented with different train/test split schemes and initializations to obtain the best classifying model. Although we were limited with a small sized training set of 200 images, using state-of-the-art image processing and data augmentation methods we obtained a high accuracy of 0.94 for 11 distinct whales. This project is served as an friendly interface to dive deep into the field of image recognition with Convolutional Neural Networks.Conference Object Next-Generation Data Storage: Transistor and Dna(Institute of Electrical and Electronics Engineers Inc., 2018) Pusane, Ali E.; Arslan, Şuayb Şefik; Ashrafi, Reza A.With the generation of diverse data growing at exponential rates, investigating better digital storage media is inevitable. Currently, one solution is the utilization of solid-state based memory devices, which offer several desirable characteristics, including very fast write/read operations, scalability, and reduced fabrication costs. However, with the increased need for long term and large storage space, their data retention capabilities drastically decline. Another emerging storage technology on the horizon is the biotechnological based DNA storage, which renders a phenomenal storage capacities. In this paper, basics of these two promising storage technologies are reviewed and their potential future trends are discussed. © 2018 IEEE.

